There comes a time that, when playing around with your Azure Management Group hierarchy, you lock yourself out of your Tenant Root Group.
This has huge implications when performing any kind of management task on your management group or underlying subscriptions. You won’t be able to perform read/write operations, including moving subscriptions from one management group to another.

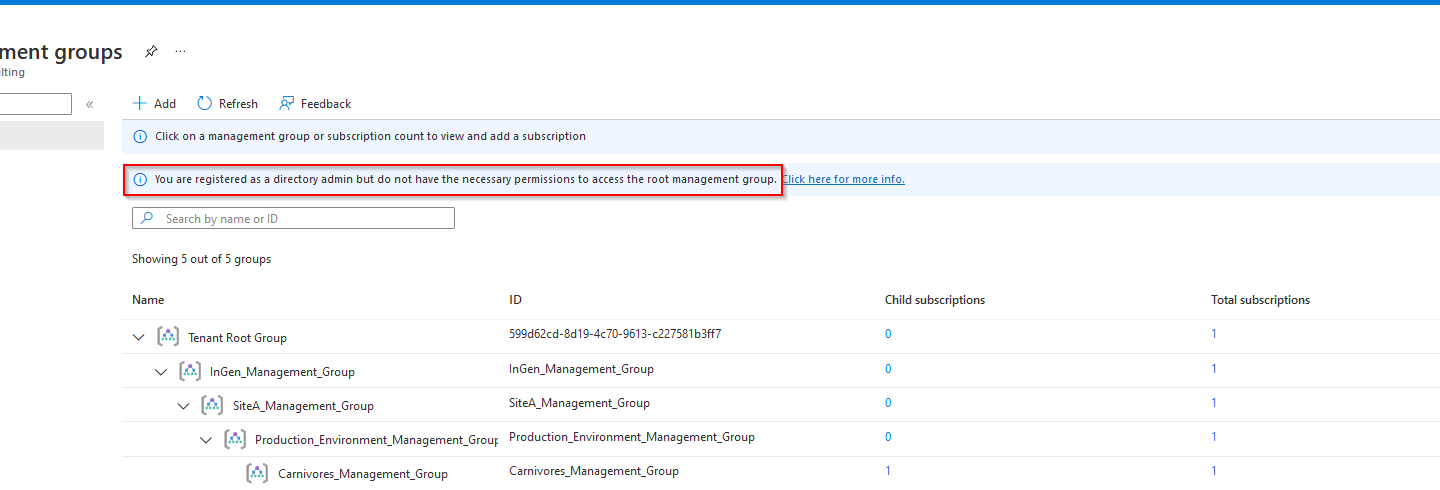
How did I found out I didn’t have sufficient permissions (anymore)? Well, the small informational message should’ve caught my attention right from the start. However, for some reason, it didn’t. So if you see this message, “You are registered as a directory admin but do not have the necessary permission to access the root management group.” Make sure to check the following.

Now, what was I actually doing when I found out? I was deploying and testing a management group hierarchy for an upcoming session. When I decided to delete my entire hierarchy without moving the subscriptions back to the root tenant group. Because.. yes, sometimes you just want to go “YOLO.” Everything went south, of course, and I ended up having 0 to no access to my management groups.
Additional quick tip: Move subscriptions first, then delete/move management groups one by one.
Things to verify before starting with Management Groups
To regain access to your management group’s hierarchy, a couple of key role assignments are advised. Have a look at the steps below to be able to manage your subscriptions and management groups again.
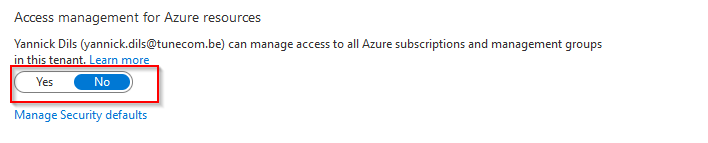
1. Enable the “Access Management for Azure Resources” for your global administrators.
=> Azure Active Directory => Properties (note: all of your Global Administrators will gain access to your Azure Resources)

2. Assign the Hierarchy Settings Administrator role
This role assignments gives your read/write access on your management group hierarchy.

New-AzRoleAssignment -SignInName "<your admin account>" -Scope "/" -RoleDefinitionName "Hierarchy Settings Administrator"
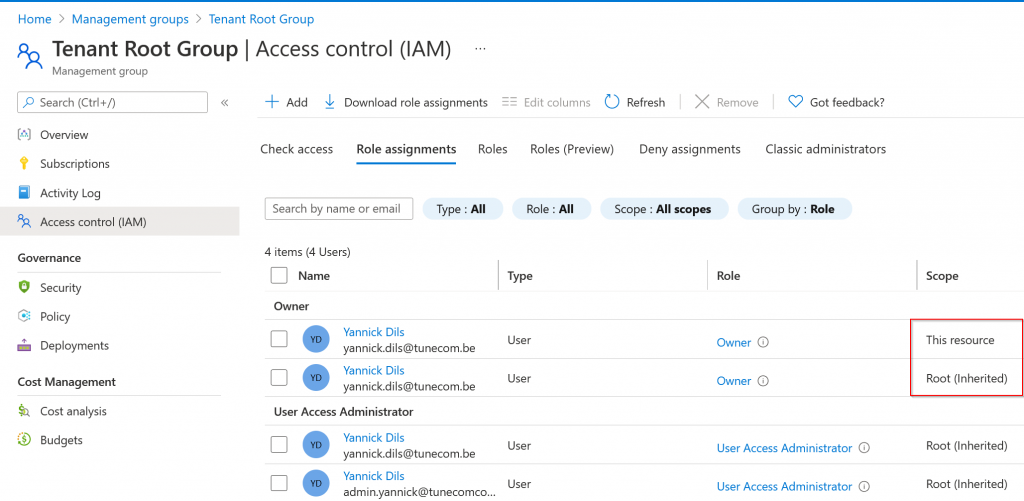
3. Assign the owner/contributor role on your Tenant Root Group.
This will inherit to all management groups and subscriptions connected to your Tenant Root Group.
New-AzRoleAssignment -SignInName "<your admin account>" -Scope "/" -RoleDefinitionName "Owner"
4. Assign the User Access Administrator role on your Tenant Root Group.
By elevating access as an User Access Administrator, you can assign any Azure role to other service principals to manage the hierarchy

New-AzRoleAssignment -SignInName "<your admin account>" -Scope "/" -RoleDefinitionName "User Access Administrator"
After having performed the above recommendations, you should now be able to perform read/write actions again.

Thank you!
Thank you for reading through this blog post. I hope you liked the quick tip, which can help you when you’ve accidentally locked yourself out of your management group hierarchy.
If you encounter any new insights, feel free to drop me a comment or contact me via mail or other social media channels.